http://mediafilter.org/caq/cryptogate/
FOR AT LEAST HALF A CENTURY, THE US HAS BEEN INTERCEPTING AND DECRYPTING THE TOP SECRET DOCUMENTS OF MOST OF THE WORLD'S GOVERNMENTS
It may be the greatest intelligence scam of the century: For decades, the US has routinely intercepted and deciphered top secret encrypted messages of 120 countries. These nations had bought the world's most sophisticated and supposedly secure commercial encryption technology from Crypto AG, a Swiss company that staked its reputation and the security concerns of its clients on its neutrality. The purchasing nations, confident that their communications were protected, sent messages from their capitals to embassies, military missions, trade offices, and espionage dens around the world, via telex, radio, teletype, and facsimile. They not only conducted sensitive albeit legal business and diplomacy, but sometimes strayed into criminal matters, issuing orders to assassinate political leaders, bomb commercial buildings, and engage in drug and arms smuggling. All the while, because of a secret agreement between the National Security Agency (NSA) and Crypto AG, they might as well have been hand delivering the message to Washington. Their Crypto AG machines had been rigged so that when customers used them, the random encryption key could be automatically and clandestinely transmitted with the enciphered message. NSA analysts could read the message traffic as easily as they could the morning newspaper. The cover shielding the NSA-Crypto AG relationship was torn in March 1992, when the Iranian military counterintelligence service arrested Hans Buehler, Crypto AG's marketing representative in Teheran. The Iranian government charged the tall, 50ish businessman with spying for the "intelligence services of the Federal Republic of Germany and the United States of America." "I was questioned for five hours a day for nine months," Buehler says. "I was never beaten, but I was strapped to wooden benches and told I would be beaten. I was told Crypto was a spy center" that worked with foreign intelligence services. Despite prolonged interrogation, Buehler-who had worked for Crypto AG for 13 years and was on his 25th trip to Iran -apparently maintained his ignorance. "I didn't know that the equipment was bugged, otherwise the Iranians ould have gotten it out of me by their many _methods._ " With millions of dollars in contracts and a major international spy operation at stake, the company was eager to make the incident and Buehler go away, even though the salesman had brought in 40 percent of Crypto's 100 million Swiss franc sales revenue. Crypto bought Buehler's freedom with a $1 million payment to the Iranians, returned him to Switzerland, and then, astonishingly, fired him and ordered the bewildered salesman to repay the bond. The cover-up backfired, however, when current and former Crypto employees came to Buehler's defense and shared their first-hand knowledge of manipulated cipher equipment. "I hold proofs [sic] of the rigging of code machines," said an unidentified former Crypto AG engineer. "Fifteen years ago, I saw American and German engineers doctoring our machines. It took me some time until I was certain about the manipulations. The proofs: technical documents. ... I put them in a bank safety deposit box. Then I informed the federal prosecutors_ office in Berne. There were many conversations. Suddenly, these contacts were broken off and the affair petered out." The engineer told another reporter: the schemes and the cipher keys were created by them [NSA and BND (Bundesnacrichtendienst-the German intelligence service)]. I immediately, discreetly, notified the Swiss prosecutors. There was an investigation. I was never able to find out the result.
Today, the Buehler affair brings everything out in the open again. And, I'm afraid. What happened to Hans Buehler could happen to any other salesperson of Crypto AG. It's not a question of attacking this company; it's a question of saving lives. ... When the Swiss media began to reveal the background of Buehler's story, Crypto AG responded with a lawsuit in an attempt to quash the story and muzzle Buehler. The suit was settled days before former Crypto engineers were to testify that they thought the machines had been altered. The parties agreed not to disclose the settlement and Crypto sought to reassure its clients. Informed sources in Switzerland and the Middle East confirmed that Crypto AG settled because it, and the NSA and BND, didn_t want to reveal anything in court. Nevertheless, the damage to Crypto AG's credibility was already done. Customers from Saddam Hussein to the Pope grew nervous. Informed of the details around the Hans Buehler incident, the Vatican Ñ which uses Swiss cipher machines to secure diplomatic communications transmitted from the Holy See to the many papal nuncios around the world-showed a marked lack of charity. An official branded the perpetrators "bandits!"
|
|
|
|
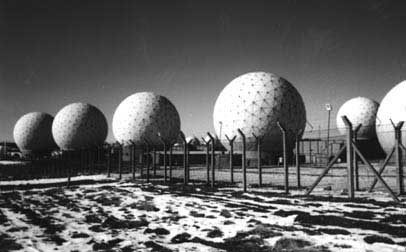
After Hans Buehler was arrested in Iran on spying chrges, the Crypto AG image of neutrality suffered and various nations reexamined their security arrangements. |
|
SWISS CHEESE NEUTRALITY
Although the Iranians may have been technically wrong about Buehler's complicity in the massive deception, they were right that something was rotten at Crypto AG. And even before the firing of Hans Buehler, some of Cypto's engineers were ambivalent about secret deals with the NSA. "At first, I was idealistic," said Juerg Spoerndli, who left Crypto in 1994. "But I adapted quickly. ... The new aim was to help Big Brother USA look over these countries_ shoulders. We_d say, _It's better to let the USA see what these dictators are doing._ " Soon, however, Spoerndli grew apprehensive over the manipulation. "It's still an imperialistic approach to the world. I don_t think it's the way business should be done." Ruedi Hug, another former Crypto AG engineer, was also critical. "I feel betrayed," he declared. "They always told us, _We are the best. Our equipment is not breakable, blah, blah, blah. ... Switzerland is a neutral country._ "
Apparently not. A document released in 1995 by Britain's Public Records Office indicates that Switzerland and nato concluded a secret deal in 1956. The "Top Secret" document, dated February 10, 1956, with the reference "prem 11/1224," was written by the famous British World War II figure, Field Marshal Bernard L. Montgomery. While "Monty" was a vice-commander of nato, he discussed a secret alliance with Swiss Defense Minister Paul Chaudet. In peacetime, Switzerland would be officially neutral, but in wartime, it would side with nato. A US document released in 1995 shows Switzerland's importance to US national security. A Presidential directive on national security prepared for President Truman states that "Switzerland ... delivers precision instruments and other materials necessary for the armament of the USA and NATO countries [emphasis added]." Germany's BND, too, has apparently cooperated with the US encryption rigging scheme through Siemens Defense Electronics Group of Munich.
A previous director of Siemens called Crypto AG a "secret Siemens daughter," while a former Crypto AG financial director said, "the owner of the firm [Crypto] is the Federal Republic [of Germany]." The Siemens connection to Crypto was remarkably incestuous. Siemens provided technical assistance for the machine manipulation process. Suspicion about the German electronics giant's role in Crypto's operations was heightened when it was reported that Siemens helped raise the $1 million to spring Buehler from his Teheran prison cell. In fact, after revelations of the Crypto-Siemens association hit the Swiss press, Crypto's managing director Michael Grupe informed the employees that the advisory board to Crypto's board of directors was being dissolved. The two advisers-Alfred Nowosad and Helmut Wiesner-were both full-time Siemens employees. With the world media describing the company as a silent partner of German and American signals intelligence (sigint) agencies around the world, Grube announced that "Crypto is changing its profile." The German government's contribution to the encryption rigging scheme also included its pressuring another Swiss firm, Gretag Data Systems AG, to allow a "red thread" program to be installed in the encryption software. "Red threading" is the software equivalent of sending in a Greek Trojan horse.18 Once owned by AT&T, this encryption manufacturer was acquired in 1995 by Information Resources Engineering (IRE), Inc. of Baltimore, Maryland.19 Interestingly, IRE is staffed by a number of ex-NSA cryptographic engineers. A third Swiss encryption company, Info Guard AG, was fully acquired by Crypto AG on June 16, 1994. Info Guard, which had been 50 percent owned by Crypto AG, primarily sells encryption units to banks in Switzerland and abroad.
Although German and American sigint agencies were involved in manipulating Crypto's cipher machines, Motorola, one of the NSA's major US contractors, performed the actual technical lteration, according to a former Crypto AG chief engineer who was personally involved in the manipulation process.
|
|
|
Boris Hagelin and one of his early cryptographic machines. |
|
CRYPTO HUDDLE
Once the cipher machines were rigged to include the secret decryption key, the BND and NSA codebreakers could use the transmitted key to read any message sent by Crypto AG's 120 country customers. One previous Crypto AG employee contends that all developmental Crypto AG equipment had to be sent for approval to the NSA and to the German Central Cipher Bureau (Zentralstelle für Chiffrierung [ZfCH]), now the Federal Information Security Agency (Bundesamt für Sicherheit in der Informationstechnik [BSI] which is also Department 62 of the BND) in Bad Godesberg, near Bonn. In other cases, Crypto AG was apparently forced to market encryption equipment manufactured in the US, sent to Crypto, and passed off as Swiss equipment.
In the 1970s, as Crypto was moving from electro-mechanical to computerized crypto units, a former Crypto AG engineer in Switzerland inspected one of the first prototype computerized machines sent from the US. He remarked that since the code could be easily broken, he found the machine useless. But when he told his superiors that he could improve the encryption process if he was given access to the mathematical functions, two US cryptographic "experts" refused to disclose the information.

According to a confidential Crypto AG memorandum, one of the NSA "experts" may have been Nora L. Mackabee, an NSA cryptographer who is now retired on a horse farm in Maryland along with her husband Lester, another retired NSA employee.
Between August 19 and 20, 1975, three Crypto AG engineers huddled with Mackabee (identified as representing "IA" Ñ most likely "intelligence agency") along with three Motorola engineers and one other American, Herb Frank. One Motorola engineer recalled that Frank was probably from another US intelligence agency based in northern Virginia but described him as a non-technical person who seemed to be making the administrative arrangements for Mackabee.
Crypto engineer Juerg Spoerndli, who was responsible for designing the firm's encryption equipment, had heard from older engineers about the visits in earlier years by mysterious Americans. He concluded that NSA was ordering the design changes through German intermediaries. He confirmed the manipulation and admitted that in the late 1970s, he was "ordered to change algorithms under mysterious circumstances"25 to weaken his cipher units.
|
PRIVACY? HA!
Although the Buehler incident lent credence to the NSA Trojan Horse theory, it was not the first time that suspicions were raised. Teheran had become concerned in 1987 when US official claimed "conclusive evidence that Iran ordered the kidnapping" of ABC News Beirut correspondent Charles Glass.26 Washington's alleged proof was coded Iranian diplomatic cables Ñ intercepted by the NSA Ñ between Teheran and the Hezbollah (Party of God) terrorist group in Lebanon via Iran's embassies in Beirut and Damascus. The next year, when a terrorist bomb brought down PanAm Flight 103 over Lockerbie, Scotland, it seems the NSA gained information by intercepting the communications of Iranian Interior Minister Ali Akbar Mohtashemi. It was apparently these messages that implicated Iran, not Libya. One intelligence summary, prepared by the US Air Force Intelligence Agency, cites Iran's Mohtashemi as the mastermind. Released in redacted form pursuant to a Freedom of Information Act (foia) request by lawyers for the bankrupt Pan American Airlines, it states: Mohtashemi is closely connected with the Al Abas and Abu Nidal terrorist groups. He is actually a long-time friend of Abu Nidal. He has recently paid 10 million dollars in cash and gold to these two organizations to carry out terrorist activities and was the one who paid the same amount to bomb PanAm Flight 103 in retaliation for the U.S. shoot-down of the Iranian Airbus. Mohtashemi has also spent time in Lebanon. An Israeli intercept of Iranian diplomatic coded communications between Mohtashemi's Interior Ministry in Teheran and the Iranian embassy in Beirut (where Mohtashemi once served as ambassador) revealed Ñ more than two years before Buehler was arrested by Iran Ñ that the Shi_ite cleric transferred $1.2 to $2 million used for the bombing of PanAm 103 to the Popular Front for the Liberation of Palestine-General Command headed by Ahmed Jibril. Such revelations must have made the Iranians extremely suspect of the security of their diplomatic traffic. The role of Israel may be explained by a little-reported intelligence alliance. NSA maintains a link with the Israeli sigint entity, "Department 8200," located in northern Tel Aviv at Herzliya. The sigint link is said to involve the British Government Communications Headquarters (gchq) base on Cyprus. Israel's ability to crack the Iranian Crypto AG codes indicates that Israel had access to the key decoding programs. The ease with which the West was reading Iranian coded transactions obviously meant that someone in Israel's sigint services possessed the decryption keys. Then in 1992, Buehler was arrested. As the Swiss authorities struggled to put the pieces together, they at first believed that the Iranian secret services were retaliating for the arrest in Switzerland of Zeynold Abedine Sarhadi, an employee of the Iranian embassy in Berne and a nephew of former Iranian President Hashemi Rafsanjani. Swiss police had arrested Sarhadi in early 1992 and were planning to extradite him to France to face trial for the 1991 assassination in Paris of former Iranian Prime Minister Shahpour Bakhtiar. On August 7, 1991, one day before Bakhtiar was found dead with his throat slit, the Teheran headquarters of the Iranian Intelligence Service, vevak, transmitted a coded message to Iranian diplomatic missions in London, Paris, Bonn, and Geneva, inquiring "Is Bakhtiar dead?" The Iranians concluded from Western press reports that British and American sigint operators had intercepted and decoded the message (as reported by L_Express of Paris) and knew that Teheran was behind the assassination. They realized that their code had been broken,30 looked to their Crypto AG cipher machines, and picked up Buehler. According to one European source, they may also have been tipped off by Stasi files of the ex-East German regime that found their way to Iran and revealed the Crypto AG ruse. In any case, the Iranians immediately began grilling prisoner 01228-1 about the role he and his company played in giving Iranian and Libyan codes to the US. Iran knew that Bakhtiar's assassination had compromised the intelligence functions of the Iranian UN mission and embassy in Geneva. The NSA had already identified one of the assassins, Mohammed Azadi, from intercepts of his phone calls from a pay phone in the town of Annecy in Savoy and an Istanbul apartment to the Iranian diplomatic mission in Geneva. On December 6, 1994, a special French terrorism court convicted two Iranians of murdering Bakhtiar, but strangely, it acquitted Sarhadi. "Justice has not been entirely served [for] reasons of state," complained Bakhtiar's widow bitterly. Those "reasons" may have included a tacit agreement among France, Switzerland, the German BND, and the NSA to spare Sarhadi in order to avoid producing captured transmissions and preserve the questionable secrecy surrounding the Crypto AG cipher manipulation program. It was not only the "rogue states" that were targeted.
|
During the sensitive Anglo-Irish negotiations of 1985, the NSA's British counterpart, the gchq, was able to decipher the coded diplomatic traffic being sent between the Irish embassy in London and the Irish Foreign Ministry in Dublin. It was reported in the Irish press that Dublin had purchased a cryptographic system from Crypto AG worth more than a million Irish pounds. It was also reported that the NSA routinely monitored and deciphered the Irish diplomatic messages. Later, during the Falklands War, British gchq operators were able to decrypt classified Argentine message traffic because the Argentineans were using rigged Crypto AG cipher machines. Former British Foreign Office minister Ted Rowlands publicly stated that gchq had penetrated Argentine diplomatic codes.
US: CRYPTO BULLY
If it turns out that the extent of communications interception is as broad as suspected, the international implications are profound. Every country in the world that used secure communications is potentially affected. Some have sought to abandon Crypto AG, but found their options limited. The US had at times required purchase of specific machines as a condition for favors. Pakistan was allegedly granted American military credits with only one provision, that it buy its encryption equipment from Crypto AG. Additionally, "It is not unheard of for NSA to offer preferential export treatment to a company if it builds a back door into its equipment," says one person with long experience in the field. "I_ve seen it. I_ve been in the room." Several countries abandoned Crypto AG but failed to ensure secrecy. The Libyans switched to Gretag units after the NSA cited secret communications to allege Libyan involvement in the 1986 La Belle disco bombing in West Berlin. One senior US official said the fact that the Libyans were making their codes more difficult to crack would "make our job tougher." But the NSA seemed to have the Gretag base covered as well. According to one knowledgeable cryptographic industry expert, NSA's program to co-opt the services of encryption manufacturrs probably extends to all those within reach of NSA operatives. US cryptographic companies would be definite candidates for such participation. The NSA program also likely extends to companies in nato and pro-US countries which have close relationships with GCHQ, NSA, and the BND. Even neutral countries_ firms are not off-limits to NSA manipulations. A former Crypto AG employee confirmed that high-level US officials approached neutral European countries and argued that their cooperation was essential to the Cold War struggle against the Soviets. The NSA allegedly received support from cryptographic companies Crypto AG and Gretag AG in Switzerland, Transvertex in Sweden, Nokia in Finland, and even newly-privatized firms in post-Communist Hungary.39 In 1970, according to a secret German BND intelligence paper, supplied to the author, the Germans planned to "fuse" the operations of three cryptographic firms-Crypto AG, Grattner AG (another Swiss cipher firm), and Ericsson of Sweden. Securocrats often turn to the boogeyman of "rogue" nations in order to justify the expense and ethical necessity of eavesdropping on all forms of international communication, but in reality many intercepts involve messages by neutral or allied nations. NSA's 1993 release of the World War II era "magic" intercepts under foia pressure revealed that US military intelligence read not only messages by Axis nations, but also intercepted and decrypted the top secret communications of Allied and neutral nations. Switzerland was among the more than 30 countries whose messages were being read. Since Swiss-made cipher machines were used by many governments at the time, it is likely that the US has been reading such messages for over half a century. An early example is the use of top secret intercepts by the US delegation to the 1945 founding convention of the United Nations in San Francisco. Fifty years of intercepted communication have given the US and its co-conspirators trade, diplomatic, economic and strategic advantages. By intercepting the "bottom line" negotiating positions of foreign governments, they have been able to shape international treaties and negotiations in their own favor: They will know, for example, the exact health status of the king of Saudi Arabia, the secret financial transactions of the president of Peru, the negotiating position of South Africa's trade delegation to the World Trade Organization, or the anti-abortion strategy of the Pope in the United Nations. Such information, presented daily to the president and the secretary of state in their intelligence briefings, is extremely useful and allows the US to play high-stakes diplomatic poker with a mirror behind everyone else's back.